QUESTION 61
Drag and Drop Question
You are evaluating the implementation of a second Edge Transport server named EDGE2 in the Amsterdam office. You need to recommend which tasks must be performed to ensure that email messages can be sent by the organization if a single Edge Transport server fails. Which three actions should you include in the recommendation?
To answer, move the three appropriate actions from the list of actions to the answer area and arrange them in the correct order.
QUESTION 62
You need to recommend which type of group must be used to create the planned department lists.
Which type of group should you recommend?
A. Universal Distribution
B. Dynamic Distribution
C. Global Security
D. Universal Security
Answer: A
Explanation:
A
Universal Distribution
Mail-enabled universal distribution groups (also called distribution groups) can be used only to distribute messages.
NOT B
A dynamic distribution group is a distribution group that uses recipient filters and conditions to derive its membership at the time messages are sent.
http://technet.microsoft.com/en-us/library/bb123722(v=exchg.150).aspx
Use the EAC to create a dynamic distribution group
As ExamTester from Netherlands commented below
But the Fabrikam case asks that users must be able to add and remove themselves from the distribution group. This is not possible using a dynamic group since membership is dynamically calculated based on attributes
Use this explanation for NOT B
http://technet.microsoft.com/en-us/library/bb201680(v=exchg.150).aspx
You can’t use Exchange Server 2013 to create non-universal distribution groups.
Mail-enabled non-universal groups were discontinued in Exchange Server 2007 and can exist only if they were migrated from Exchange 2003 or earlier versions of Exchange.
Seems to contradict the above.
NOT C D
In Exchange, all mail-enabled groups are referred to as distribution groups, whether they have a security context or not.
QUESTION 63
You need to recommend which tasks must be performed to meet the technical requirements of the research and development (R&D) department. Which two tasks should you recommend? (Each correct answer presents part of the solution. Choose two.)
A. Create a new global address list (GAL) and a new address book policy.
B. Modify the permissions of the default global address list (GAL), and then create a new GAL.
C. Run the Update AddressList cmdlet.
D. Run the Set-Mailbox cmdlet.
E. Create an OAB virtual directory.
Answer: AD
Explanation:
NOT B
Need an address book policy
NOT C
Update AddressList cmdlet
Use the Update-AddressList cmdlet to update the recipients included in the address list that you specify.
EXAMPLE 1
This example updates the recipients of the address list building4 and under the container All Users\Sales.
Update-AddressList -Identity “All Users\Sales\building4”
NOT E
Will not resolve the issue
Need an address book policy and to assign this policy to users.
A
Address book policies (ABPs) allow you to segment users into specific groups to provide customized views of your organization’s global address list (GAL).
When creating an ABP, you assign a GAL, an offline address book (OAB), a room list, and one or more address lists to the policy.
You can then assign the ABP to mailbox users, providing them with access to a customized GAL in Outlook and Outlook Web App.
The goal is to provide a simpler mechanism to accomplish GAL segmentation for on-premises organizations that require multiple GALs.
D
After you create an address book policy (ABP), you must assign it to mailbox users. Users aren’t assigned a default ABP when their user account is created.
If you don’t assign an ABP to a user, the global address list (GAL) for your entire organization will be accessible to the user through Outlook and Outlook Web App.
This example assigns the ABP All Fabrikam to the existing mailbox user [email protected].
Set-Mailbox -Identity [email protected] -AddressBookPolicy “All Fabrikam”
QUESTION 64
You are testing the planned implementation of Domain Security. You discover that users fail to exchange domain-secured email messages. You open the Exchange Management Shell and discover the output shown in the exhibit. (Click the Exhibit button.)
![clip_image002[6] clip_image002[6]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D221/clip_image0026_thumb.jpg)
You need to ensure that users can exchange email messages by using Domain Security. Which two parameters should you modify by using the Set-SendConnector cmdlet? (Each correct answer presents part of the solution. Choose two.)
A. tlsauthlevel
B. requiretls
C. ignorestarttls
D. tlsdomain
E. domainsecureenabled
F. smarthostauthmechanism
Answer: BE
Explanation:
NOT TLSAUTHLEVEL
The TlsAuthLevel parameter specifies the TLS authentication level that is used for outbound TLS connections established by this Send connector. Valid values are:
EncryptionOnly: TLS is used only to encrypt the communication channel. No certificate authentication is performed.
CertificateValidation: TLS is used to encrypt the channel and certificate chain validation and revocation lists checks are performed.
DomainValidation: In addition to channel encryption and certificate validation, the Send connector also verifies that the FQDN of the target certificate matches the domain specified in the TlsDomain parameter. If no domain is specified in the TlsDomain parameter, the FQDN on the certificate is compared with the recipient’s domain.
You can’t specify a value for this parameter if the IgnoreSTARTTLS parameter is set to $true, or if the RequireTLS parameter is set to $false.
NOT ignorestarttls
The IgnoreSTARTTLS parameter specifies whether to ignore the StartTLS option offered by a remote sending server.
This parameter is used with remote domains. This parameter must be set to $false if the RequireTLS parameter is set to $true. Valid values for this parameter are $true or $false.
NOT tlsdomain
The TlsDomain parameter specifies the domain name that the Send connector uses to verify the FQDN of the target certificate when establishing a TLS secured connection.
This parameter is used only if the TlsAuthLevel parameter is set to DomainValidation.
A value for this parameter is required if:
The TLSAuthLevel parameter is set to DomainValidation.
The DNSRoutingEnabled parameter is set to $false (smart host Send connector).
NOT smarthostauthmechanism
The SmartHostAuthMechanism parameter specifies the smart host authentication mechanism to use for authentication with a remote server.
Use this parameter only when a smart host is configured and the DNSRoutingEnabled parameter is set to $false.
Valid values are None, BasicAuth, BasicAuthRequireTLS, ExchangeServer, and ExternalAuthoritative.
All values are mutually exclusive. If you select BasicAuth or BasicAuthRequireTLS, you must use the AuthenticationCredential parameter to specify the authentication credential.
QUESTION 65
You need to recommend which recovery solution will restore access to all of the mailboxes in AccountingDB if EX1 fails. The solution must restore access to email messages as quickly as possible.
Which recovery solution should you recommend?
A. On EX2, create a new mailbox database. Restore the database files, and then mount the database.
Run the New-MailboxRestoreRequest cmdlet for all of the mailboxes in the database.
B. On EX2, create a new mailbox database. Restore the database files, and then mount the database.
Run the Set-Mailbox cmdlet for all of the mailboxes in the database.
C. On replacement hardware, run setup /mode:recoverserver. Restore the database files, and then mount
the database. Run the Set-Mailbox cmdlet.
D. On replacement hardware, run setup /mode:recoverserver. Restore the database files, and then mount
the database. Run the New-MailboxRestoreRequest cmdlet for all of the mailboxes in the database.
Answer: A
Explanation:
http://technet.microsoft.com/en-us/library/ee332351%28v=exchg.150%29.aspx
QUESTION 66
You have an Exchange Server 2013 organization. All user mailboxes have an In-Place Archive enabled.
You need to identify which email message types can be archived by using a retention policy. Which message type or types should you identify? (Each correct answer presents part of the solution. Choose all that apply.)
A. calendar items
B. mail items
C. note items
D. task items
E. contact items
Answer: BCE
QUESTION 67
Hotspot Question
You need to recommend which script the administrators must run to create the reports required to meet the technical requirements. Which script should you recommend? To answer, select the appropriate script in the answer area.
QUESTION 68
You need to create an exclusion for two helpdesk RBAC (Role Based Access Control) groups to not have access to managers. You will need to pick 3 powershell commands from the available choices
A. New-ManagementRole, New-ManagementScope,Set-ManagementScope (Guessed)
B. New-ManagementScope, RecipientRestrictionFilter ,New-ManagementRoleAssignment (Guessed)
C. New-ManagementScope, New-ManagementRoleAssignment, CustomRecipientWriteScope (Guessed)
D. Unsure of commands and correct answer
Answer: D
QUESTION 69
Drag and Drop Question
You have an Exchange Server 2013 organization that contains two servers. The servers are configured as shown in the following table.
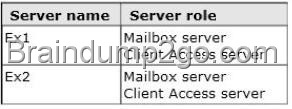
You need to create a new database availability group (DAG) that contains EX1 and EX2.
Which three actions should you perform?
To answer, move the three appropriate actions from the list of actions to the answer area and arrange them in the correct order.
QUESTION 70
You have an Exchange Server 2013 organization that contains one Client Access server. The Client Access server is accessible from the Internet by using a network address translation (NAT) device. You deploy an additional Client Access server. You also deploy an L4 hardware load balancer between the Client Access servers and the NAT device. After deploying the hardware load balancer, you discover that all of the Exchange Server traffic is directed to a single Client Access server. You need to ensure that the hardware load balancer distributes traffic evenly across both Client Access servers. What should you do?
A. Change the default route of the Client Access servers to point to the hardware load balancer.
B. Configure the NAT device to pass the original source IP address of all connections from the Internet.
C. Configure the Client Access servers to have a second IP address and web site. Create the Exchange
virtual directories in the new sites.
D. Configure SSL offloading on the hardware load balancer and the Client Access servers.
Answer: B
Explanation:
Level 4 Load Balancer
A load balancer is a server computer with a very specialized operating system tuned to manage network traffic using user-created rules. Enterprises and hosting companies rely on load-balancing devices to distribute traffic to create highly available services L4 load balancing is fairly simple, two servers sharing the same IP address. You get redirected to the less-busy server. The most popular Layer 4 load balancing techniques are:
round-robin
weighted round-robin
least connections
weighted least connections
NOT A
http://pdfs.loadbalancer.org/Microsoft_Exchange_2013_Deployment_Guide.pdf If there was no NAT device and the load balancer was completing the NAT translation then there maybe some merit in this answer option. B is a better answer given this scenario.
NOT C
No need to configure the Client Access servers to have a second IP address.
NOT D
Not required in this scenario
SSL offloading relieves a Web server of the processing burden of encrypting and/or decrypting traffic sent via SSL, the security protocol that is implemented in every Web browser. The processing is offloaded to a separate device designed specifically to perform SSL acceleration or SSL termination.
Correct Answer B
When using source NAT, the client IP address is not passed to the load balanced server. The insertion of the Client IP address into the header allows the exchange servers to see the IP that made the connection.
http://pdfs.loadbalancer.org/Microsoft_Exchange_2013_Deployment_Guide.pdf
If you want to pass the Microsoft 70-341 Exam sucessfully, recommend to read latest Microsoft 70-341 Dump full version.

![clip_image002[4] clip_image002[4]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D221/clip_image0024_thumb.jpg)
![clip_image002[8] clip_image002[8]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D221/clip_image0028_thumb.jpg)
![clip_image002[10] clip_image002[10]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D221/clip_image00210_thumb.jpg)
![clip_image002[12] clip_image002[12]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D221/clip_image00212_thumb.jpg)
![clip_image002[14] clip_image002[14]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D221/clip_image00214_thumb.jpg)
