QUESTION 41
You have an Exchange Server 2013 organization that contains two servers named EX1 and EX2. EX1 and EX2 are the members of a database availability group (DAG) named DAG1. EX1 and EX2 each contain a copy of a mailbox database named DB1. DB1 is configured to retain deleted items for 120 days. At the end of each month, the mailbox databases on EX1 are backed up to tape. The monthly backups are retained for two years. A user named User1 has a mailbox in DB1. User1 discovers that a mailbox folder that contained important email messages was deleted more than six months ago. You need to recover the deleted mailbox folder without affecting any other users who have mailboxes in DB1. Which three actions should you perform? (Each correct answer presents part of the solution.
Choose three.)
A. Run the New-MaiboxRestoreRequestcmdlet.
B. Run the New-MailboxDatabasecmdlet and specify the Recovery parameter.
C. Restore DB1 from the tape backup to an alternate location.
D. Restore DB1 from the tape backup to the database’s original location.
E. Run the New-Mailbox cmdlet and specify the Recovery parameter.
Answer: ABC
Explanation:
Recovery Database
A recovery database is a special kind of mailbox database that allows you to mount a restored mailbox database and extract data from the restored database as part of a recovery operation. You can use the New-MailboxRestoreRequest cmdlet to extract data from a recovery database. After extraction, the data can be exported to a folder or merged into an existing mailbox. Recovery databases enable you to recover data from a backup or copy of a database without disturbing user access to current data.
A
New-MaiboxRestoreRequestcmdlet
Use the New-MailboxRestoreRequest cmdlet to restore a soft-deleted or disconnected mailbox. This cmdlet starts the process of moving content from the soft-deleted mailbox, disabled mailbox, or any mailbox in a recovery database into a connected primary or archive mailbox. For information about the parameter sets in the Syntax section below, see Syntax.
EXAMPLE 1
To create a restore request, you must provide the DisplayName, LegacyDN, or MailboxGUID for the softdeleted or disabled mailbox. This example uses the Get-MailboxStatistics cmdlet to return the DisplayName, LegacyDN, MailboxGUID, and DisconnectReason for all mailboxes on mailbox database MBD01 that have a disconnect reason of SoftDeleted or Disabled. Get-MailboxStatistics -Database MBD01 | Where { $_.DisconnectReason -eq “SoftDeleted” -or $_. DisconnectReason -eq “Disabled” } | Format-List LegacyDN, DisplayName, MailboxGUID, DisconnectReason
This example restores the source mailbox with the MailboxGUID 1d20855f-fd54-4681-98e6- e249f7326ddd on mailbox database MBD01 to the target mailbox with the alias Ayla. New-MailboxRestoreRequest -SourceDatabase “MBD01” -SourceStoreMailbox 1d20855f-fd54-4681- 98e6-e249f7326ddd -TargetMailbox Ayla
B
Use the New-MailboxDatabase cmdlet to create a mailbox database object in the database container in Active Directory.
For information about the parameter sets in the Syntax section below, see Syntax.
EXAMPLE 1
This example creates the mailbox database MailboxDatabase01.
This example also specifies where to create the .edb database file, which is different than the default location.
New-MailboxDatabase -Name “MailboxDatabase01” -EdbFilePath
D:\DatabaseFiles\MailboxDatabase01.edb
The Recovery parameter specifies that the new database is designated as a recovery database.
NOT D
Need to recover data from a backup or copy of a database without disturbing user access to current data.
Therefore restore to an alternate location.
NOT E
No recovery parameter exists for the New-Mailbox cmdlet.
QUESTION 42
You have an Exchange Server 2010 organization. All users connect to their mailbox by using Microsoft Outlook 2013 and Outlook Web App. All client connections to Exchange Server use the name mail.contoso.com. You deploy Exchange Server 2013 to the organization, you move all of the users to Exchange Server 2013, and then you decommission all of the Exchange Server 2010 servers. The users report that when they open Outlook 2013, they receive a certificate warning message. The users do not receive a certificate error message or a certificate warning message when they open Outlook Web App. You need to prevent the certificate warning message from occurring when the users open Outlook 2013. Which cmdlet should you run?
A. Set-ClientAccessServer
B. New-ExchangeCertficiate
C. New-ClientAccessArray
D. Import-ExchangeCertificate
Answer: A
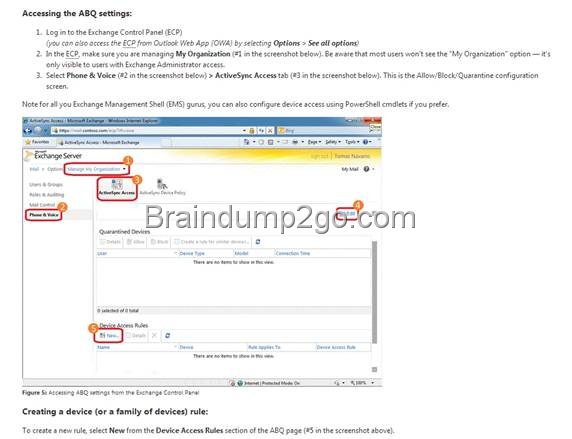
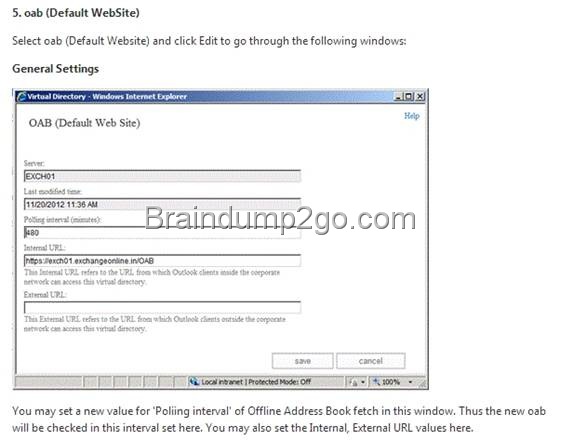
QUESTION 43
Your network contains an Active Directory forest. The forest contains two sites named Montreal and New York. You have an Exchange Server 2013 organization that contains a Mailbox server and a Client Access server in each site. The users in the New York site report that the offline address book (OAB) is not updated after an extended WAN outage between the sites. The Montreal site contains the OAB generation server. You need to ensure that the New York site users download the OAB from a server in the New York site. Which two cmdlets should you run? (Each correct answer presents part of the solution. Choose two.)
A. Set-Mailbox
B. New-OfflineAddressBook
C. New-Mailbox
D. New-OabVirtualDirectory
E. Set-OfflineAddressBook
Answer: AC
Explanation:
A
Set-Mailbox
Use the Set-Mailbox cmdlet to modify the settings of an existing mailbox. You can use this cmdlet for one mailbox at a time.
To perform bulk management, you can pipeline the output of various Get- cmdlets (for example, the Get-Mailbox or Get-User cmdlets) and configure several mailboxes in a single-line command. You can also use the Set-Mailbox cmdlet in scripts.
For information about the parameter sets in the Syntax section below, see Syntax.
Step2: Enable OABGen capability
Set-Mailbox -Arbitration oabs -OABGen $true
http://technet.microsoft.com/en-us/library/aa996345(v=exchg.150).aspx
Provision Recipients for Offline Address Book Downloads
To specify which OAB is downloaded by linking the OAB directly to a recipient’s mailbox, use the following syntax.
Set-Mailbox -Identity <MailboxIDParameter> -OfflineAddressBook <OfflineAddressBookIdParameter>
Better for this question (but the option is not covered:)
Use the Shell to specify the OAB that multiple recipients will download
This example specifies that all user mailboxes in the United States for Contoso will download the OAB Contoso United States.
Get-User -ResultSize Unlimited -Filter { Company -eq “Contoso” -and RecipientType -eq “UserMailbox” } | Where { $_.CountryOrRegion -eq “United States”} | Set-Mailbox -OfflineAddressBook “Contoso United States”
NOT B
New-OfflineAddressBook
Use the New-OfflineAddressBook cmdlet to create an offline address book (OAB).
EXAMPLE 1
This example uses two commands to create the OAB named OAB_AgencyB that includes all address lists where AgencyB is part of the name. With the settings shown, an OAB is generated by myserver.contoso.com on Mondays and Wednesdays from 01:00 (1:00 A.M.) to 02:00 (2:00 A.M.). The command also creates the default OAB for the organization.
$a = Get-AddressList | Where {$_.Name -Like “*AgencyB*”
New-OfflineAddressBook -Name “OAB_AgencyB” -Server myserver.contoso.com -AddressLists $a -Schedule “Mon.01:00-Mon.02:00, Wed.01:00-Wed.02:00”
C
New-Mailbox
Use the New-Mailbox cmdlet to create a user in Active Directory and mailbox-enable this new user.
Step1: Create a new arbitration mailbox
New-Mailbox -Arbitration -Name “OAB New York” -Database DB2NewYork -UserPrincipalName [email protected] –DisplayName “OAB Mailbox for New York”
EXAMPLE 1
This example creates a user Chris Ashton in Active Directory and creates a mailbox for the user. The mailbox is located on Mailbox Database 1. The password must be reset at the next logon. To set the initial value of the password, this example creates a variable ($password), prompts you to enter a password, and assigns that password to the variable as a SecureString object.
$password = Read-Host “Enter password” -AsSecureString
New-Mailbox -UserPrincipalName [email protected] -Alias chris -Database “Mailbox Database 1” -Name ChrisAshton -OrganizationalUnit Users -Password $password -FirstName Chris -LastName Ashton -DisplayName “Chris Ashton” -ResetPasswordOnNextLogon $true
NOT D
New-OabVirtualDirectory
Use the New-OABVirtualDirectory cmdlet to configure a server as a web distribution point for an offline address book (OAB).
EXAMPLE 1
This example creates an OAB virtual directory on CASServer01 and configures the distribution service to poll the generation server every two hours.
New-OABVirtualDirectory -Server CASServer01 -PollInterval 120
NOT E
Set-OfflineAddressBook
Use the Set-OfflineAddressBook cmdlet to modify offline address book (OAB) settings.
EXAMPLE 1
This example changes the name of the OAB.
Set-OfflineAddressBook -Identity “\Default Offline Address Book” -Name “My Offline Address Book”
QUESTION 44
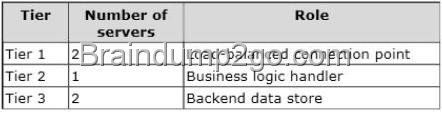
Your network contains an Active Directory forest. The forest contains one domain. The domain contains two sites and three domain controllers. The sites and domain controllers are configured as shown in the following table.
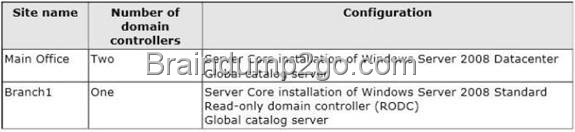
The sites connect to each other by using a WAN link. You have an Exchange Server 2013 organization that contains two servers in the Main Office site. In Branch1, you plan to deploy one server to the Exchange Server 2013 organization. You need to ensure that all of the Exchange Server services in Branch1 are available if the WAN link fails after the planned deployment. What should you do?
A. Create a site link bridge, and then configure Branch1 as a hub site.
B. Replace the domain controller in Branch1 with an RODC that runs Windows Server 2012.
C. Replace the domain controller in Branch1 with a writable domain controller that runs a Server Core
installation of Windows Server 2008.
D. Create an additional site link, and then configure Branch1 as a hub site.
Answer: C
Explanation:
Site link bridge
A site link bridge connects two or more site links and enables transitivity between site links. Each site link in a bridge must have a site in common with another site link in the bridge. The Knowledge Consistency Checker (KCC) uses the information on each site link to compute the cost of replication between sites in one site link and sites in the other site links of the bridge. Without the presence of a common site between site links, the KCC also cannot establish direct connections between domain controllers in the sites that are connected by the same site link bridge. By default, all site links are transitive.
![clip_image002[4] clip_image002[4]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_CDC7/clip_image0024_thumb.jpg)
This figure illustrates an organization’s hub-and-spoke network topology, consisting of two hub sites (A and B) and six satellite sites (C through H). The site links between all sites are named A-B, A-C, A- D, A-E, B-F, B-G, and B-H.
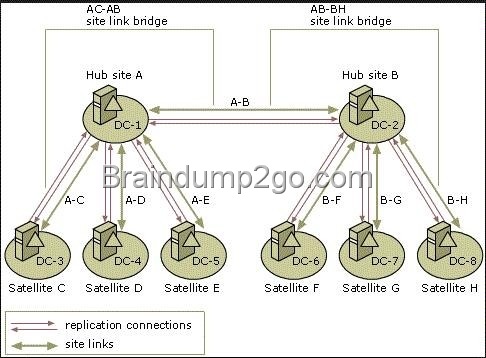
Hub Site
A hub site is based on having large numbers of outgoing links NOT A B D
If you want to install or operate any Exchange 2013 server in a site, you must have a writable global catalog in the same AD site.
Be aware that no versions of Exchange Server will make use of RODC or the Global Catalog server on a RODC although Exchange will work in the presence of RODC as long as writable versions of domain controllers and GCs are available
C
If you want to install or operate any Exchange 2013 server in a site, you must have a writable global catalog in the same AD site.
The Global Catalog is the central repository of information about objects in a tree or forest but with a limited number of each objects attribute.
The domain controller that holds a copy of the Global Catalog is the Global Catalog Server. The global catalog server makes it possible to search the entire AD DS forest without referrals to the domain controller that stores the target of the search. The global catalog server is also required for searching and processing domain logons in forests where universal groups is available Be aware that no versions of Exchange Server will make use of RODC or the Global Catalog server on a RODC although Exchange will work in the presence of RODC as long as writable versions of domain controllers and GCs are available
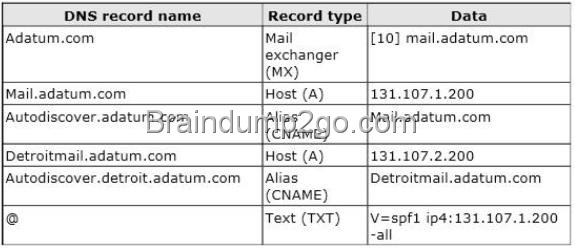
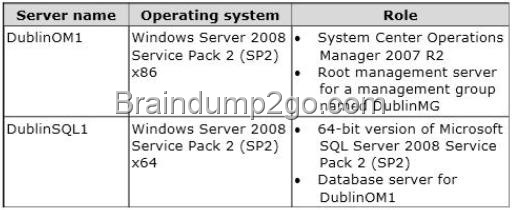
QUESTION 45
Your company has a main office site and a disaster recovery site. The two sites connect to each other by using redundant WAN links. Each site connects directly to the Internet. Each site contains one Exchange Server 2013 server that is accessible from the Internet. The company uses the ©ontoso.com email address suffix. The DNS records that can be resolved from the Internet are configured as shown in the following table.
![clip_image001[4] clip_image001[4]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_CDC7/clip_image0014_thumb.jpg)
When the Internet link at the main office site fails, the company cannot receive incoming email from the Internet. You need to ensure that incoming email from the Internet is delivered to Server1. Incoming email from the Internet must be delivered to Server2 if Server1 is unavailable. What should you create?
A. A CNAME record for the name mail.contoso.com that resolves to server2.contoso.com
B. An MX record that has a cost of 20 and resolves to mail.contoso.com
C. An MX record that has a cost of 20 and resolves to server2.contoso.com
D. An A record for the name mail.contoso.com that resolves to 131.107.101.1
Answer: C
Explanation:
CNAME record
A CNAME record is an abbreviation for Canonical Name record and is a type of resource record in the Domain Name System (DNS) that specifies that the domain name is an alias of another, canonical domain name. Here “canonical” usually means: a more generally accepted or standard name.
For example, if there is a DNS zone as follows:
NAME TYPE VALUE
————————————————–
bar.example.com. CNAME foo.example.com.
foo.example.com. A 192.0.2.23
MX record
A mail exchanger record (MX record) is a type of resource record in the Domain Name System that specifies a mail server responsible for accepting email messages on behalf of a recipient’s domain, and a preference value used to prioritize mail delivery if multiple mail servers are available. The set of MX records of a domain name specifies how email should be routed with the Simple Mail Transfer Protocol (SMTP).
A Record
An A (address) record is a DNS record that can be used to point your domain name and host names to a static IP address.
NOT A B D
Need to increase the cost associated with the MX record of Server2 so that Server1 is preferred over Server2 but Server2 will be used if Server1 is not available.
C
Need to increase the cost associated with the MX record of Server2 so that Server1 is preferred over Server2 but Server2 will be used if Server1 is not available.
QUESTION 46
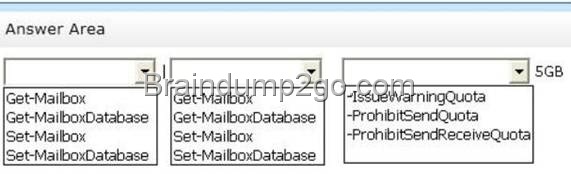
Drag and Drop Question
You have an Exchange Server 2013 organization named adatum.com. The organization contains a server named Server1. Server1 is a member of a Database Availability Group (DAG) named DAG1. You have a user named Sales1 in the Sales department. You need to prevent Sales1 from submitting more than 75 email messages per minute to the Exchange Server organization by using Microsoft Outlook. Which three commands should you run in sequence? (To answer, move the appropriate three commands from the list of commands to the answer area and arrange them in the correct order.)
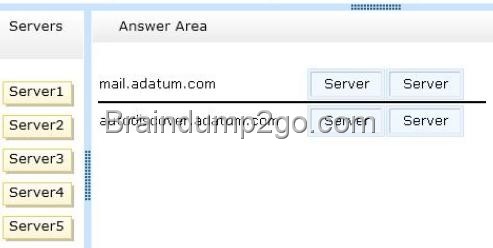
QUESTION 47
Drag and Drop Question
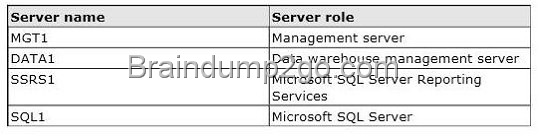
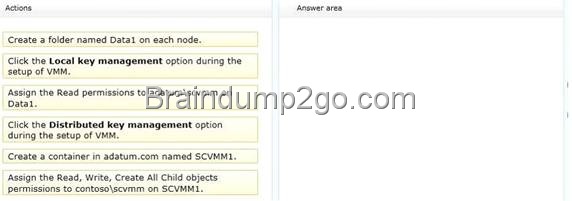
You have an Exchange Server organization that contains three servers. The servers are configured as shown in the following table.
![clip_image002[10] clip_image002[10]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_CDC7/clip_image00210_thumb.jpg)
You need to create a new database availability group (DAG) that contains EX1 and EX2. Which three actions should you perform in sequence? (To answer, move the appropriate three actions from the list of actions to the answer area and arrange them in the correct order.)
![clip_image002[14] clip_image002[14]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_CDC7/clip_image00214_thumb.jpg)
Explanation:
Box 1: Add the Exchange Trusted Subsystem universal security group to the local Administrators group on Server1.
Box 2: Create a new DAG and specify Server1 as the file share witness.
Box 3: Add EX1 and EX2 to the DAG.
Note:
* A database availability group (DAG) is a set of up to 16 Microsoft Exchange Server 2013 Mailbox servers that provide automatic database-level recovery from a database, server, or network failure. When a Mailbox server is added to a DAG, it works with the other servers in the DAG to provide automatic, database-level recovery from database, server, and network failures.
* You can specify a name for the DAG and the witness server that you want to use, and leave the Witness directory field empty. In this scenario, the task will create the default witness directory on the specified witness server.
* If the witness server you specify isn’t an Exchange 2013 or Exchange 2010 server, you must add the Exchange Trusted Subsystem universal security group to the local Administrators group on the witness server. These security permissions are necessary to ensure that Exchange can create a directory and share on the witness server as needed.
Reference: Exchange 2013, Create a Database Availability Group
QUESTION 48
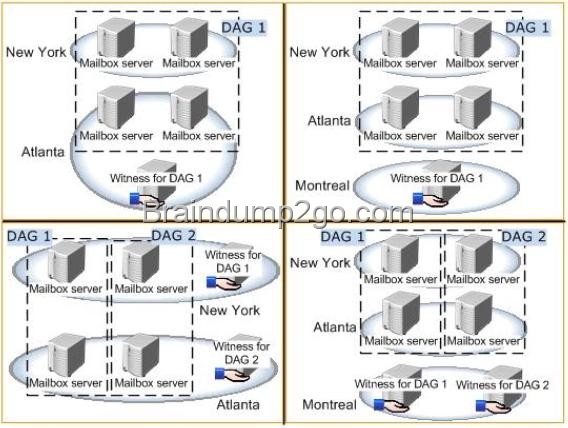
You have an Exchange Server 2013 organization that contains two Mailbox servers named MBX1 and MBX2. You create a database availability group (DAG) named DAG1. DAG1 is configured as shown in the exhibit. You need to ensure that replication only occurs over the replication network. Which two commands should you run? (Each correct answer presents part of the solution. Choose two.)
A. Set-DatabaseAvailabilityGroup Dag1 -ManualDagNetworkConfiguration $true
B. Set-DatabaseAvailabilityGroup Dag1 -ManualDagNetworkConfiguration $false
C. Set-DatabaseAvailabilityGroupNetwork MapiDagNetwork -ReplicationEnabled $false
D. Set-DatabaseAvailabilityGroupNetwork ReplicationDagNetwork01 -ReplicationEnabled $true
Answer: BC
Explanation:
You need to ensure that replication only occurs over the replication network.
If you would like to ‘force’ replication to only go over the Replication Network, then you definately would like to disable replication on the MAPI Network, but IF the NIC on the Replication Network goes down, it will start replicating over the MAPI NIC. There is no way of blocking that behaviour and isn’t what you’d want anyway since DAGs actually cope quite fine with just 1 NIC.
DAG Networks
Each database availability group (DAG) network has several properties that you can configure, including the name of the DAG network, a description field for the DAG network, a list of subnets that are used by the DAG network, and whether the DAG network is enabled for replication. You can configure a DAG network only when automatic network configuration has been disabled for a DAG.
There are specific networking requirements that must be met for each DAG and for each DAG member. Each
DAG must have a single MAPI network, which is used by a DAG member to communicate with other servers (for example, other Exchange 2013 servers or directory servers), and zero or more Replication networks, which are networks dedicated to log shipping and seeding. Although a single network is supported, we recommend that each DAG have at least two networks: a single MAPI network and a single Replication network. This provides redundancy for the network and the network path, and enables the system to distinguish between a server failure and a network failure. Using a single network adapter prevents the system from distinguishing between these two types of failures.
![clip_image002[18] clip_image002[18]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_CDC7/clip_image00218_thumb.jpg)
MAPI
MAPI stands for Messaging Application Programming Interface, and it gives programs the ability to send email using your email program to do the actual sending.
Set-DatabaseAvailabilityGroup
The Set-DatabaseAvailabilityGroup cmdlet enables you to manage DAG properties that can’t be managed from the Exchange Administration Center (EAC), such as configuring network discovery, selecting the TCP port used for replication, and enabling datacenter activation coordination (DAC) mode.
Set-DatabaseAvailabilityGroupNetwork
Use the Set-DatabaseAvailabilityGroupNetwork cmdlet to configure a network for a database availability group (DAG).
You can configure a variety of network properties, such as the name for the network, a description of the network, a list of one or more subnets that comprise the network, and whether the network is enabled for replication (log shipping and seeding).
You need to be assigned permissions before you can run this cmdlet. Although all parameters for this cmdlet are listed in this topic, you may not have access to some parameters if they’re not included in the permissions assigned to you.
C
Ensures that you can configure a DAG network by turning the automatic configuration off.
The ManualDagNetworkConfiguration parameter
Specifies whether DAG networks should be automatically configured. If this parameter is set to False, DAG networks are automatically configured. If this parameter is set to True, you must manually configure DAG networks.
You can configure a DAG network only when automatic network configuration has been disabled for a DAG.
Need to manually configure the DAG NETWORK
NOT D
Need to turn the automatic DAG configuration off.
The ManualDagNetworkConfiguration parameter Specifies whether DAG networks should be automatically configured. If this parameter is set to False, DAG networks are automatically configured. If this parameter is set to True, you must manually configure DAG networks. You can configure a DAG network only when automatic network configuration has been disabled for a DAG.
NOT A
Does not disable the replication over the MAPI network as required in this scenario B
Disables replication over the MAPI network as required in this scenario
QUESTION 49
You have an Exchange Server 2013 organization that contains a server named Server1. Server1 has an IP address of 10.1.100.16 and is configured to use a default gateway of 10.1.100.1. You deploy a hardware load balancer that is configured to use the IP addresses of 192.168.101.31 and 10.1.100.31.
A user named User1 has a client computer that has an IP address of 102.168.101.201. User1 reports that he cannot view his mailbox by using Outlook Web App. When you review the IIS logs on Server1, you discover the following information:
![]()
You need to ensure that User1 can access his mailbox successfully from Outlook Web App. What are two possible ways to achieve this goal? (Each correct answer presents a complete solution. Choose two.)
A. Configure the hardware load balancer to use the same certificate as the certificate used on Server1.
B. Configure the hardware load balancer to use source NAT (SNAT).
C. Configure the computer of User1 to ignore response headers.
D. Modify the default gateway of Server1.
Answer: BD
Explanation:
Source NAT
When using source NAT, the client IP address is not passed to the load balanced server. The insertion of the Client IP address into the header allows the servers to see the IP that made the connection They are then able to return the requested information correctly B
Configuring the hardware load balancer to use source NAT (SNAT) will resolve the problem.
D
Changing the default gateway of Server1 to that of the hardware load balancer will ensure that the connection to Server1 will be returned via the network load balancer and out to User1 NOT A
Not a certificate problem
NOT C
NOT a http response header issue
HTTP response header
The information, in the form of a text record, that a Web server sends back to a clients browser in response to receiving an HTTP request.
The response header contains the date, size and type of file that the server is sending back to the client and also data about the server itself.
The header is attached to the files being sent back to the client.
QUESTION 50
You have an Exchange Server 2013 organization that is configured to filter email messages for spam and malware. You need to modify the schedule for applying updates to the anti-spam and the antimalware definitions. Which command should you run?
A. Update-MalwareFilteringServer.ps1
B. Set-MalwareFilteringServer
C. Set-SenderFilterConfig
D. Update-SafeList
Answer: B
Explanation:
NOT A
Microsoft Exchange Server 2013 administrators can manually download anti-malware engine and definition (signature) updates.
Update-MalwareFilteringServer.ps1 used in manual updates not schedule updates.
NOT C
Not used for spam and malware updates.
Use the Set-SenderFilterConfig cmdlet to modify the Sender Filter agent configuration.
EXAMPLE 1
This example makes the following modifications to the Sender Filter agent configuration:
It enables blocking of blank senders.
It blocks messages from lucernepublishing.com and all subdomains. It adds [email protected] and [email protected] to the blocked senders list without affecting any existing entries.
Set-SenderFilterConfig -BlankSenderBlockingEnabled $true -BlockedDomainsAndSubdomains
lucernepublishing.com -BlockedSenders @{Add=”[email protected]”,”[email protected]”} NOT D
Use the Update-SafeList cmdlet to update the safelist aggregation data in Active Directory. Safelist aggregation data is used in the built-in anti-spam filtering in Microsoft Exchange. EdgeSync replicates
safelist aggregation data to Edge Transport servers in the perimeter network.
EXAMPLE 1
This example updates Safe Senders List data for the single user [email protected].
Update-Safelist [email protected]
B
Set-MalwareFilteringServer
Use the Set-MalwareFilteringServer cmdlet to configure the Malware agent settings in the Transport service on a Mailbox server.
Example 1
This example sets the following Malware agent settings on the Mailbox server named Mailbox01:
Sets the update frequency interval to 2 hours
Sets the time to wait between resubmit attempts to 10 minutes Set-MalwareFilteringServer Mailbox01 -UpdateFrequency 120 -DeferWaitTime 10
If you want to pass the Microsoft 70-341 Exam sucessfully, recommend to read latest Microsoft 70-341 Dump full version.
![clip_image002[6] clip_image002[6]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_CDC7/clip_image0026_thumb.jpg)
![clip_image002[8] clip_image002[8]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_CDC7/clip_image0028_thumb.jpg)
![clip_image002[12] clip_image002[12]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_CDC7/clip_image00212_thumb.jpg)
![clip_image002[16] clip_image002[16]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_CDC7/clip_image00216_thumb.jpg)


![clip_image002[4] clip_image002[4]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_ECE5/clip_image0024_thumb.jpg)
![clip_image002[8] clip_image002[8]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_ECE5/clip_image0028_thumb.jpg)
![clip_image002[10] clip_image002[10]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_ECE5/clip_image00210_thumb.jpg)
![clip_image002[12] clip_image002[12]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_ECE5/clip_image00212_thumb.jpg)
![clip_image001[4] clip_image001[4]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_ECE5/clip_image0014_thumb.jpg)
![clip_image001[6] clip_image001[6]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_ECE5/clip_image0016_thumb.jpg)
![clip_image001[8] clip_image001[8]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_ECE5/clip_image0018_thumb.jpg)
![clip_image002[14] clip_image002[14]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_ECE5/clip_image00214_thumb.jpg)
![clip_image001[10] clip_image001[10]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_ECE5/clip_image00110_thumb.jpg)
![clip_image001[12] clip_image001[12]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_ECE5/clip_image00112_thumb.jpg)
![clip_image002[16] clip_image002[16]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_ECE5/clip_image00216_thumb.jpg)
![clip_image002[18] clip_image002[18]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_ECE5/clip_image00218_thumb.jpg)
![clip_image001[14] clip_image001[14]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_ECE5/clip_image00114_thumb.jpg)
![clip_image002[20] clip_image002[20]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_ECE5/clip_image00220_thumb.jpg)
![clip_image001[4] clip_image001[4]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E9C2/clip_image0014_thumb.jpg)
![clip_image001[6] clip_image001[6]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E9C2/clip_image0016_thumb.jpg)
![clip_image002[4] clip_image002[4]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E9C2/clip_image0024_thumb.jpg)
![clip_image001[8] clip_image001[8]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E9C2/clip_image0018_thumb.jpg)
![clip_image001[10] clip_image001[10]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E9C2/clip_image00110_thumb.jpg)
![clip_image002[6] clip_image002[6]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E9C2/clip_image0026_thumb.jpg)
![clip_image002[8] clip_image002[8]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E9C2/clip_image0028_thumb.jpg)
![clip_image001[12] clip_image001[12]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E9C2/clip_image00112_thumb.jpg)
![clip_image002[10] clip_image002[10]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E9C2/clip_image00210_thumb.jpg)
![clip_image002[12] clip_image002[12]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E9C2/clip_image00212_thumb.jpg)
![clip_image002[14] clip_image002[14]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E9C2/clip_image00214_thumb.jpg)
![clip_image002[16] clip_image002[16]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E9C2/clip_image00216_thumb.jpg)
![clip_image002[18] clip_image002[18]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E9C2/clip_image00218_thumb.jpg)
![clip_image002[20] clip_image002[20]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E9C2/clip_image00220_thumb.jpg)
![clip_image002[22] clip_image002[22]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E9C2/clip_image00222_thumb.jpg)
![clip_image002[24] clip_image002[24]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E9C2/clip_image00224_thumb.jpg)
![clip_image001[4] clip_image001[4]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E60B/clip_image0014_thumb.jpg)
![clip_image001[6] clip_image001[6]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E60B/clip_image0016_thumb.jpg)
![clip_image001[8] clip_image001[8]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E60B/clip_image0018_thumb.jpg)
![clip_image001[10] clip_image001[10]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E60B/clip_image00110_thumb.jpg)
![clip_image001[12] clip_image001[12]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E60B/clip_image00112_thumb.jpg)
![clip_image001[14] clip_image001[14]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E60B/clip_image00114_thumb.jpg)
![clip_image002[4] clip_image002[4]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E60B/clip_image0024_thumb.jpg)
![clip_image002[6] clip_image002[6]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E60B/clip_image0026_thumb.jpg)
![clip_image002[8] clip_image002[8]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E60B/clip_image0028_thumb.jpg)
![clip_image002[10] clip_image002[10]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E60B/clip_image00210_thumb.jpg)
![clip_image001[16] clip_image001[16]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E60B/clip_image00116_thumb.jpg)
![clip_image002[12] clip_image002[12]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E60B/clip_image00212_thumb.jpg)
![clip_image002[14] clip_image002[14]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E60B/clip_image00214_thumb.jpg)
![clip_image001[4] clip_image001[4]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E3E3/clip_image0014_thumb.jpg)
![clip_image002[4] clip_image002[4]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E3E3/clip_image0024_thumb.jpg)
![clip_image001[6] clip_image001[6]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E3E3/clip_image0016_thumb.jpg)
![clip_image001[8] clip_image001[8]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E3E3/clip_image0018_thumb.jpg)
![clip_image001[10] clip_image001[10]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E3E3/clip_image00110_thumb.jpg)
![clip_image002[6] clip_image002[6]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E3E3/clip_image0026_thumb.jpg)
![clip_image001[14] clip_image001[14]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E3E3/clip_image00114_thumb.jpg)
![clip_image001[16] clip_image001[16]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E3E3/clip_image00116_thumb.jpg)
![clip_image002[8] clip_image002[8]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E3E3/clip_image0028_thumb.jpg)
![clip_image002[10] clip_image002[10]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E3E3/clip_image00210_thumb.jpg)
![clip_image002[12] clip_image002[12]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E3E3/clip_image00212_thumb.jpg)
![clip_image002[14] clip_image002[14]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E3E3/clip_image00214_thumb.jpg)
![clip_image002[16] clip_image002[16]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E3E3/clip_image00216_thumb.jpg)
![clip_image001[18] clip_image001[18]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E3E3/clip_image00118_thumb.jpg)
![clip_image001[20] clip_image001[20]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E3E3/clip_image00120_thumb.jpg)
![clip_image001[22] clip_image001[22]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E3E3/clip_image00122_thumb.jpg)
![clip_image001[24] clip_image001[24]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E3E3/clip_image00124_thumb.jpg)
![clip_image001[26] clip_image001[26]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E3E3/clip_image00126_thumb.jpg)
![clip_image002[4] clip_image002[4]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70247Dump_CE6A/clip_image0024_thumb.jpg)
![clip_image001[4] clip_image001[4]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70247Dump_CDA0/clip_image0014_thumb.jpg)
![clip_image001[4] clip_image001[4]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70247Dump_CC70/clip_image0014_thumb.jpg)
![clip_image001[6] clip_image001[6]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70247Dump_CC70/clip_image0016_thumb.jpg)
![clip_image001[11] clip_image001[11]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70247Dump_CF36/clip_image00111_thumb.jpg)
![clip_image001[13] clip_image001[13]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70247Dump_CF36/clip_image00113_thumb.jpg)