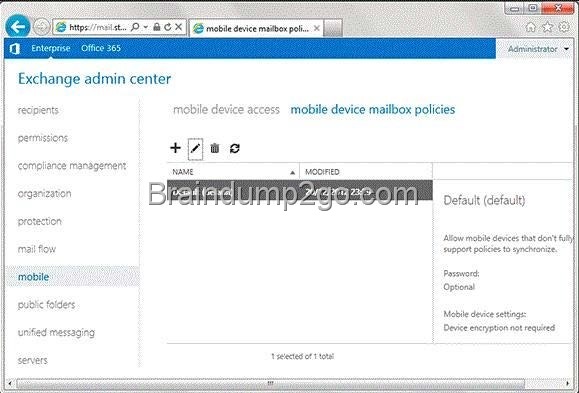
QUESTION 71
Hotspot Question
You discover that one of the Client Access servers in the New York office does not trust the standalone CA. You need to ensure that all of the users who have Windows Phone devices can connect successfully to their mailbox. In which node should you install the root CA certificate? To answer, select the appropriate node in the answer area.
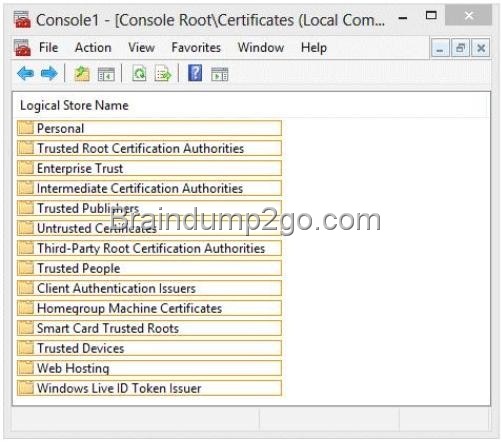
Answer:
![clip_image001[4] clip_image001[4]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D3F6/clip_image0014_thumb.jpg)
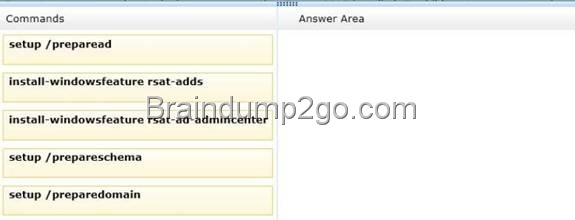
QUESTION 72
You have an Exchange Server 2013 organization that contains five servers. All users connect to their mailbox by using a mobile device. All of the users in the finance department are in an organizational unit (OU) named OU1. You need to prevent the finance users from accessing the extended storage on their mobile device. What should you do?
A. Create a new mobile device mailbox policy, and then run the Set-CasMailbox cmdlet.
B. Create a new device access rule, and then run the Set-Mailbox cmdlet.
C. Create a new mobile device mailbox policy, and then run the Set-Mailbox cmdlet.
D. Create a new device access rule, and then run the Set-CasMailbox cmdlet.
Answer: A
Explanation:
Set-CASMailbox cmdlet
Use the Set-CASMailbox cmdlet to set attributes related to client access for Microsoft Exchange ActiveSync, Microsoft Office Outlook Web App, POP3, and IMAP4 for a specified user. The Set-CASMailbox cmdlet operates on one mailbox at a time. You can configure properties for Outlook Web App, Exchange ActiveSync, POP3, and IMAP4 by using this cmdlet. You can configure a single property or multiple properties by using one statement.
Set-Mailbox cmdlet.
Use the Set-Mailbox cmdlet to modify the settings of an existing mailbox. You can use this cmdlet for one mailbox at a time.
Mobile device mailbox policy
In Microsoft Exchange Server 2013, you can create mobile device mailbox policies to apply a common set of policies or security settings to a collection of users. After you deploy Exchange ActiveSync in your Exchange 2013 organization, you can create new mobile device mailbox policies or modify existing policies. When you install Exchange 2013, a default mobile device mailbox policy is created. All users are automatically assigned this default mobile device mailbox policy.
Device access rule
Use device access rules to allow users to synchronize their mailboxes with specific mobile device families or models.
NOT B C
Use the Set-CASMailbox cmdlet to set attributes related to client access for Microsoft Exchange ActiveSync, Microsoft Office Outlook Web App, POP3, and IMAP4 for a specified user.
NOT D
In Microsoft Exchange Server 2013, you can create mobile device mailbox policies to apply a common set of policies or security settings to a collection of users
QUESTION 73
You have an Exchange Server 2013 server that has a single mailbox database named DB1. You need to move the transaction log files of DB1. Which cmdlet should you run?
A. Move-DatabasePath
B. Move-Mailbox
C. Set-ExchangeServer
D. Set-MailboxDatabase
Answer: A
QUESTION 74
You have an Exchange Server 2013 organization named contoso.com.
Your company is Investigating a user named User1. You need to prevent User1 from permanently deleting the items in his mailbox.
What should you run?
A. Set-Mailbox User1 -LitigationHoldEnabled $true
B. Set-Mailbox User1 -ModerationEnabled $true
C. Set-Mailbox User1 -RetainDeletedItemsUntilBackup $true
D. Set-Mailbox User1 -RetentionHoldEnabled $true
Answer: A
QUESTION 75
You have an Exchange 2013 organization. You have an administrative user named Admin1. You need to ensure that Admin1 can move mailboxes in the organization. The solution must assign the minimum amount of permissions to Admin1. What should you do?
A. Create a local move request.
B. Create a custom Management role. Assign the role to Admin1.
C. Add Admin1 to the Organization Management role group.
D. Add Admin1 to the Recipient Management security group.
Answer: B
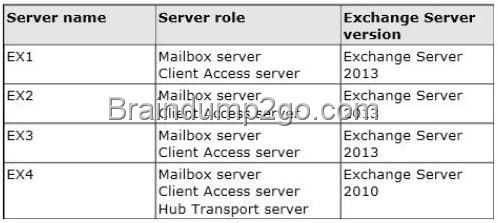
QUESTION 76
Hotspot Question
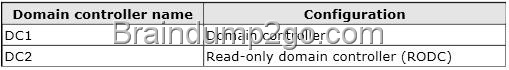
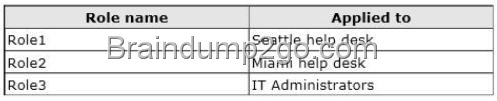
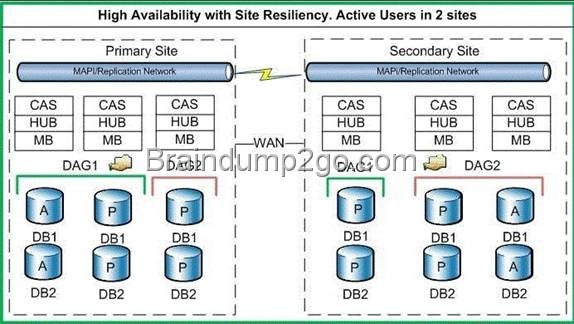
Your company has two offices. The offices are configured as shown in the following table.
![clip_image001[6] clip_image001[6]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D3F6/clip_image0016_thumb.jpg)
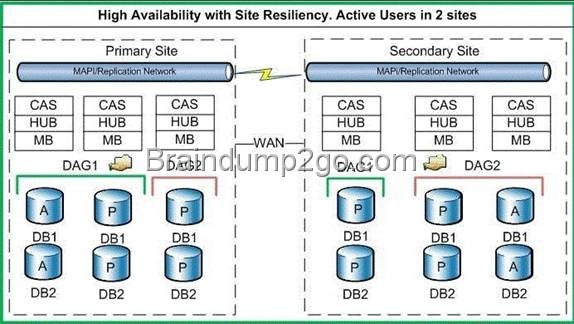
The offices connect to each other by using a WAN link that has a latency of more than 700 ms. You plan to deploy an Exchange Server 2013 organization to meet the following requirements:
– Ensure that users can access their mailbox if the WAN link fails.
– Ensure that users can access their mailbox if a single server fails.
– Ensure that users can access their mailbox if a single database fails.
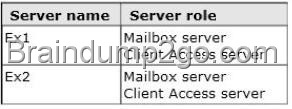
You recommend deploying one or more database availability groups (DAGs) and mailbox database copies. You need to identify which design meets the requirements for the planned deployment.
Which design should you identify?
To answer, select the appropriate design in the answer area.
![clip_image001[8] clip_image001[8]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D3F6/clip_image0018_thumb.jpg)
Answer:
![clip_image001[10] clip_image001[10]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D3F6/clip_image00110_thumb.jpg)
Explanation:
File Share Witness
The file share witness is used to establish a majority node set. This is done by create a share on a server that gets a little file place into it automatically. The server hosting the cluster resource (which in the DAG I think is the Primary Activation Manager server) keeps an open file lock on this file.
The other servers see this open file lock and interpret this as meaning another cluster node is online, healthy, and available.
A file share witness is used when the DAG contains an even number of servers within it. When you initially create the DAG you must specify the server and file location that will act as the file share witness regardless of how many servers are in the DAG (0 to start) to ensure that if you do add an even number of DAG members the FSW will be properly used.
Database Availability Group
A database availability group (DAG) is a set of up to 16 Microsoft Exchange Server 2013 Mailbox servers that provide automatic database-level recovery from a database, server, or network failure. When a Mailbox server is added to a DAG, it works with the other servers in the DAG to provide automatic, database-level recovery from database, server, and network failures. DAGs use continuous replication and a subset of Windows failover clustering technologies to provide high availability and site resilience.
Mailbox servers in a DAG monitor each other for failures. When a Mailbox server is added to a DAG, it works with the other servers in the DAG to provide automatic, database-level recovery from database failures.
When you create a DAG, it’s initially empty, and a directory object is created in Active Directory that represents the DAG. The directory object is used to store relevant information about the DAG, such as server membership information. When you add the first server to a DAG, a failover cluster is automatically created for the DAG. In addition, the infrastructure that monitors the servers for network or server failures is initiated. The failover cluster heartbeat mechanism and cluster database are then used to track and manage information about the DAG that can change quickly, such as database mount status, replication status, and last mounted location. Witness server and witness directory The witness server is a server outside the DAG that acts as a quorum voter when the DAG contains an even number of members. The witness directory is a directory created and shared on the witness server for use by the system in maintaining a quorum.
Lagged copy of a mailbox database
A Lagged Mailbox Database Copy is a mailbox database copy configured with a replay lag time value greater than 0.
A lagged database copy is one that is not updated by replaying transactions as they become available.
Instead, the transaction logs are kept for a certain period and are then replayed. The lagged database copy is therefore maintained at a certain remove to the active database and the other non-lagged database copies. If you are planning to have more than two passive database copies of a database, think about a lagged copy also as an additional protection against unpredicted situations Lagged copies aren’t considered highly available copies. Instead, they are designed for disaster recovery purposes, to protect against store logical corruption. The greater the replay lag time set, the longer the database recovery process. Depending on the number of log files that need to replayed during recovery, and the speed at which your hardware can replay them, it may take several hours or more to recover a database.
![clip_image001[12] clip_image001[12]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D3F6/clip_image00112_thumb.jpg)
The above configuration provides a symmetrical design. All four servers have the same four databases all hosted on a single disk per server.
The key is that the number of copies of each database that you have should be equal to the number of database copies per disk.
In the above example, there are four copies of each database: one active copy, two passive copies, and one lagged copy. Because there are four copies of each database, the proper configuration is one that has four copies per volume. In addition, activation preference is configured so that it’s balanced across the DAG and across each server.
For example, the active copy will have an activation preference value of 1, the first passive copy will have an activation preference value of 2, the second passive copy will have an activation preference value of 3, and the lagged copy will have an activation preference value of 4.
Lagged mailbox database copy
A passive mailbox database copy that has a log replay lag time greater than zero.
Crossed Lines
DAG Replication 1 and 2
Circled Areas
Site 1 and Site 2 (or DataCenter1 and DataCenter2)
WAN LINK between Site1 and Site2
High Availability with Site Resiliency Exchange 2010 Example
http://jaworskiblog.com/2011/05/17/exchange-2010-design-principles-for-high-availability-and-site- resiliency/
FSW is the File Share Witness
![clip_image001[14] clip_image001[14]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D3F6/clip_image00114_thumb.jpg)
ASIDE
Windows NLB is not supported across sites.
It is not recommended to use an HLB to load balance across sites. PICTURE1 OFFERS THE BEST DESIGN IN ORDER TO MEET THE SPECIFIED CRITERIA.
MORE FAULTS WITH THE OTHERS.
PICTURE1 HOWEVER DOES NOT OFFER SITE RESILIENCY.
– Ensure that users can access their mailbox if the WAN link fails.
– Ensure that users can access their mailbox if a single server fails.
– Ensure that users can access their mailbox if a single database fails.
Picture1
The DAG is NOT extended across multiple data centers in a site resilience configuration.
The design offers high availability within each site.
However if a node fails or the wan link fails the respective file share witness for each DAG is still available unlike the other 3 configurations.
Picture2
The DAG is extended across multiple data centers in a site resilience configuration.
No high availability within each site.
If the wan link is unavailable the file share witness for Site2 would be unavailable This is a split brain scenario, both sites believe that they are the rightful owner of the database, and thus would mount their respective DB’s. This would cause a divergence in data. Email could be sent to either database leaving to a difference between the databases on the respective mailbox servers.
Picture3
The DAG is extended across multiple data centers in a site resilience configuration. FSW on Site2 in the event of a wan failure means that the servers cannot contact a FSW Even number of nodes on the respective site with an inability to contact the FSW. This is a split brain scenario, both sites believe that they are the rightful owner of the database, and thus would mount their respective DB’s. This would cause a divergence in data. Email could be sent to either database leaving to a difference between the databases on the respective mailbox servers.
A file share witness is used when the DAG contains an even number of servers within it. A Node Majority quorum model is used for DAGs with an odd number of members. A Node and File Share Majority quorum is used for DAGs with an even number of members.
The DAG needs to be able to make Quorum.
When 1 node fails in Site1 and the wan link is down,1 out of 2 nodes left is not a majority. Need to be able to connect to the file share witness to obtain a majority.
Picture4
1 DAG across both sites provides site resiliency but FSW on Site1 in the event of a wan failure means that the servers cannot contact a FSW A file share witness is used when the DAG contains an even number of servers within it.
Even number of nodes on the respective site with an inability to contact the FSW. This is a split brain scenario, both sites believe that they are the rightful owner of the database, and thus would mount their respective DB’s. This would cause a divergence in data. Email could be sent to either database leaving to a difference between the databases on the respective mailbox servers.
A file share witness is used when the DAG contains an even number of servers within it. A Node Majority quorum model is used for DAGs with an odd number of members. A Node and File Share Majority quorum is used for DAGs with an even number of members.
QUESTION 77
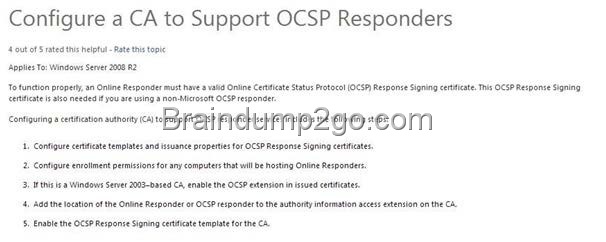
You deploy a server that has the Exchange Server 2013 Mailbox server role and Client Access server role installed. You need to configure anti-spam to meet the following requirements:
– Email messages sent from the Internet to a distribution list named Executives must be rejected.
– Email messages that contain the words casino and jackpot must be rejected, unless they were sent to [email protected].
Which three cmdlets should you run? (Each correct answer presents part of the solution. Choose three.)
A. Add ContentFilterPhrase
B. Set-ContentFilterConfig
C. Set-TransportConfig
D. Set-SenderReputationConfig
E. Set-RecipientFilterConfig
Answer: ABE
Explanation:
NOT C
Use the Set-TransportConfig cmdlet to modify the transport configuration settings for the whole Exchange organization.
This example configures the Exchange organization to redirect all journaling reports that can’t be delivered to the journaling mailbox to the email account [email protected].
Set-TransportConfig -JournalingReportNdrTo [email protected]
NOT D
Use the Set-SenderReputationConfig cmdlet to modify the sender reputation configuration on a Mailbox server or an Edge Transport server.
Sender reputation is part of the Exchange anti-spam functionality that blocks messages according to many characteristics of the sender.
Sender reputation relies on persisted data about the sender to determine what action, if any, to take on an inbound message. The Protocol Analysis agent is the underlying agent for sender reputation functionality.
When you configure anti-spam agents on an Exchange server, the agents act on messages cumulatively to reduce the number of unsolicited messages that enter the organization.
QUESTION 78
Your company named Contoso, Ltd., has an Exchange Server 2013 organization named contoso.com. The network contains an Active Directory domain. The domain contains an organizational unit (OU) named SalesOU. SalesOU contains two users named User1 and User2. Contoso purchases a domain name adatum.com. You need to change the primary SMTP address of all the users in SalesOU to use the SMTP suffix of adatum.com. The solution must not remove the contoso.com email address. Which two actions should you perform? (Each correct answer presents part of the solution. Choose two.)
A. Create a new email address policy and apply the policy to the users in SalesOU.
B. Change the default email address policy to include adatum.com.
C. Create a new remote domain for adatum.com.
D. Create a new accepted domain for adatum.com and set the domain type to Authoritative Domain.
E. Create a new accepted domain for adatum.com and set the domain type to External RelayDomain.
Answer: AD
Explanation:
NOT B
No need to change the default email policy.
Create a new email address policy
NOT C
No need for a remote domain
You can create remote domain entries to define the settings for message transfer between the Microsoft Exchange Server 2013 organization and domains outside your Exchange organization.
When you create a remote domain entry, you control the types of messages that are sent to that domain. You can also apply message format policies and acceptable character sets for messages that are sent from users in your organization to the remote domain. The settings for remote domains are global configuration settings for the Exchange organization.
The remote domain settings are applied to messages during categorization in the Transport service on Mailbox servers. When recipient resolution occurs, the recipient domain is matched against the configured remote domains. If a remote domain configuration blocks a specific message type from being sent to recipients in that domain, the message is deleted. If you specify a particular message format for the remote domain, the message headers and content are modified. The settings apply to all messages that are processed by the Exchange organization.
NOT E
Do not want to use a relay server.When you configure an external relay domain, messages are relayed to an email server that’s outside your Exchange organization and outside the organization’s network perimeter.
Typically, most Internet-facing messaging servers are configured to not allow for other domains to be relayed through them.
However, there are scenarios where you may want to let partners or subsidiaries relay email through your Exchange servers. In Exchange 2013, you can configure accepted domains as relay domains. Your organization receives the email messages and then relays the messages to another email server.
You can configure a relay domain as an internal relay domain or as an external relay domain. These two relay domain types are described in the following sections.
Corrent Answer A
Need to create a new email address policy
Corrent Answer D
There are three types of accepted domains: authoritative, internal relay, and external relay.
Configure an Accepted Domain within Your Exchange Organization as Authoritative
Applies to: Exchange Server 2013
If a domain belonging to your organization hosts mailboxes for all the recipients within an SMTP namespace, that domain is considered to be authoritative.
By default, one accepted domain is configured as authoritative for the Exchange organization.
If your organization has more than one SMTP namespace, you can configure more than one accepted domain as authoritative.
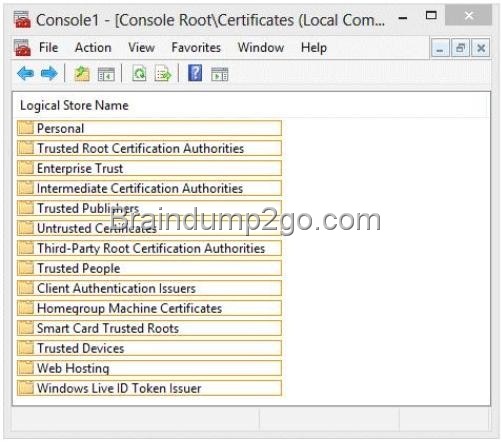
QUESTION 79
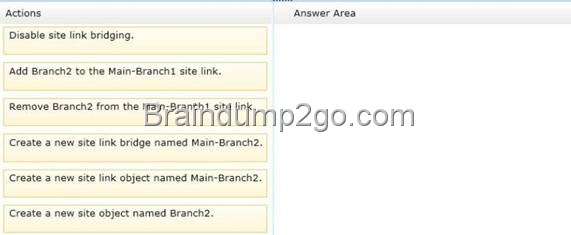
Drag and Drop Question
You have an Exchange Server 2013 organization named Contoso. The organization is configured to apply a disclaimer to all email messages sent to external recipients. Your company works with a partner company named A. Datum Corporation. A. Datum has an SMTP domain named adatum.com. You need to ensure that email messages sent to adatum.com meet the following compliance requirements:
– Messages sent to adatum.com must NOT include the disclaimer.
– Messages that contain credit card numbers must NOT be sent to adatum.com.
– If a user writes a message that contains a credit card number and the message is addressed to a recipient at adatum.com, the user must receive a notification before the message is sent.
What should you configure for each requirement?
To answer, drag the appropriate configuration to the correct requirement in the answer area. Each configuration may be used once, more than once, or not at all. Additionally, you may need to drag the split bar between panes or scroll to view content.
![clip_image002[4] clip_image002[4]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D3F6/clip_image0024_thumb.jpg)
Answer:
![clip_image002[6] clip_image002[6]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D3F6/clip_image0026_thumb.jpg)
Explanation:
Box 1: A transport rule exception
Box 2: A data loss prevention policy
Box 3: a Policy Tip
Note:
* Each transport rule can have exceptions that specify what to exclude from the condition. Exceptions typically determine a subset of criteria identified in the condition. If you use transport rules, you can specify what information you don’t want to enter or leave the organization, which individuals or groups shouldn’t be able to communicate with one another, how messages are handled based on how they are classified by the sender, and more.
* The Data loss prevention (DLP) feature in the new Exchange will help you identify, monitor, and protect sensitive information in your organization through deep content analysis. DLP is increasingly important for enterprise message systems because business critical email includes sensitive data that needs to be protected. It’s the financial information, personally identifiable information (PII) and intellectual property data that can be accidently sent to unauthorized users that keeps the CSO up all night.
* Policy Tip notification messages are displayed to users in Outlook while they are composing an email message. Policy Tip notification messages only show up if something about the sender’s email message seems to violate a DLP policy that you have in place and that policy includes a rule to notify the sender when the conditions that you establish are met.
* Incorrect: MailTips are evaluated every time a sender adds a recipient to a message. Reference: Introducing Data Loss Prevention in the New Exchange; Policy Tips
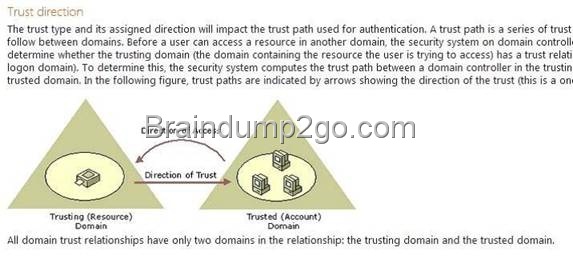
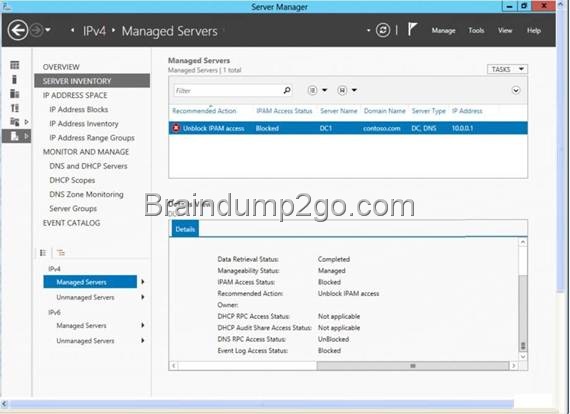
QUESTION 80
Drag and Drop Question
You have an Exchange Server 2013 organization that contains three servers named EX1, EX2, and EX3. The servers are members of a database availability group (DAG) named DAG1. A mailbox database named DB1 is replicated to all the members of DAG1.
EX3 experiences a complete hardware failure.
You need to restore EX3 on a new server.
You reset the computer account for EX3.
Which three actions should you perform next?
To answer, move the three appropriate actions from the list of actions to the answer area and arrange them in the correct order.
![clip_image002[8] clip_image002[8]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D3F6/clip_image0028_thumb.jpg)
Answer:
![clip_image002[10] clip_image002[10]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D3F6/clip_image00210_thumb.jpg)
Explanation:
Note: Use Setup /m:RecoverServer to recover a server
Retrieve any replay lag or truncation lag settings for any mailbox database copies that exist on the server being recovered by using the Get-MailboxDatabase cmdlet. (Box 1) Remove any mailbox database copies that exist on the server being recovered by using theRemove-MailboxDatabaseCopy cmdlet.
(Box 1) Remove the failed server’s configuration from the DAG by using the Remove- DatabaseAvailabilityGroupServer cmdlet.
Reset the server’s computer account in Active Directory. For detailed steps, see Reset a Computer Account.
(Box 2) Open a Command Prompt window. Using the original Setup media, run the following command.
Setup /m:RecoverServer
(Box 3) When the Setup recovery process is complete, add the recovered server to the DAG by using the Add-DatabaseAvailabilityGroupServer cmdlet.
(Box 3) After the server has been added back to the DAG, you can reconfigure mailbox database copies by using the Add-MailboxDatabaseCopy cmdlet.
* You can recover a lost server by using the Setup /m:RecoverServer switch in Microsoft Exchange Server 2013. Most of the settings for a computer running Exchange 2013 are stored in Active Directory. The /m:RecoverServer switch rebuilds an Exchange server with the same name by using the settings and other information stored in Active Directory.
Reference: Recover a Database Availability Group Member Server
If you want to pass the Microsoft 70-341 Exam sucessfully, recommend to read latest Microsoft 70-341 Dump full version.

![clip_image001[8] clip_image001[8]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_C26B/clip_image0018_thumb.jpg)
![clip_image001[18] clip_image001[18]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_C26B/clip_image00118_thumb.jpg)
![clip_image001[24] clip_image001[24]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_C26B/clip_image00124_thumb.jpg)
![clip_image001[4] clip_image001[4]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_C26B/clip_image0014_thumb.jpg)
![clip_image001[6] clip_image001[6]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_C26B/clip_image0016_thumb.jpg)
![clip_image001[10] clip_image001[10]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_C26B/clip_image00110_thumb.jpg)
![clip_image001[12] clip_image001[12]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_C26B/clip_image00112_thumb.jpg)
![clip_image001[14] clip_image001[14]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_C26B/clip_image00114_thumb.jpg)
![clip_image001[16] clip_image001[16]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_C26B/clip_image00116_thumb.jpg)

![clip_image001[20] clip_image001[20]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_C26B/clip_image00120_thumb.jpg)
![clip_image001[22] clip_image001[22]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_C26B/clip_image00122_thumb.jpg)
![clip_image001[26] clip_image001[26]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_C26B/clip_image00126_thumb.jpg)

![clip_image001[4] clip_image001[4]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_CC56/clip_image0014_thumb.jpg)
![clip_image001[6] clip_image001[6]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_CC56/clip_image0016_thumb.jpg)
![clip_image002[4] clip_image002[4]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_CC56/clip_image0024_thumb.jpg)
![clip_image001[8] clip_image001[8]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_CC56/clip_image0018_thumb.jpg)
![clip_image001[10] clip_image001[10]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_CC56/clip_image00110_thumb.jpg)
![clip_image001[12] clip_image001[12]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_CC56/clip_image00112_thumb.jpg)
![clip_image001[14] clip_image001[14]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_CC56/clip_image00114_thumb.jpg)
![clip_image001[16] clip_image001[16]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_CC56/clip_image00116_thumb.jpg)
![clip_image001[4] clip_image001[4]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_CB35/clip_image0014_thumb.jpg)
![clip_image001[6] clip_image001[6]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_CB35/clip_image0016_thumb.jpg)
![clip_image001[8] clip_image001[8]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_CB35/clip_image0018_thumb.jpg)
![clip_image001[10] clip_image001[10]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_CB35/clip_image00110_thumb.jpg)
![clip_image001[12] clip_image001[12]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_CB35/clip_image00112_thumb.jpg)
![clip_image001[14] clip_image001[14]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_CB35/clip_image00114_thumb.jpg)
![clip_image002[4] clip_image002[4]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_C9CF/clip_image0024_thumb.jpg)
![clip_image002[6] clip_image002[6]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_C9CF/clip_image0026_thumb.jpg)
![clip_image002[8] clip_image002[8]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_C9CF/clip_image0028_thumb.jpg)
![clip_image001[4] clip_image001[4]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_C9CF/clip_image0014_thumb.jpg)
![clip_image001[6] clip_image001[6]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_C9CF/clip_image0016_thumb.jpg)
![clip_image001[8] clip_image001[8]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_C9CF/clip_image0018_thumb.jpg)
![clip_image001[10] clip_image001[10]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_C9CF/clip_image00110_thumb.jpg)
![clip_image001[12] clip_image001[12]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_C9CF/clip_image00112_thumb.jpg)
![clip_image002[10] clip_image002[10]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_C9CF/clip_image00210_thumb.jpg)
![clip_image001[14] clip_image001[14]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_C9CF/clip_image00114_thumb.jpg)
![clip_image001[16] clip_image001[16]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_C9CF/clip_image00116_thumb.jpg)
![clip_image001[18] clip_image001[18]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_C9CF/clip_image00118_thumb.jpg)
![clip_image002[12] clip_image002[12]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_C9CF/clip_image00212_thumb.jpg)
![clip_image001[4] clip_image001[4]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_C821/clip_image0014_thumb.jpg)
![clip_image001[6] clip_image001[6]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_C821/clip_image0016_thumb.jpg)
![clip_image002[4] clip_image002[4]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_C821/clip_image0024_thumb.jpg)
![clip_image001[8] clip_image001[8]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_C821/clip_image0018_thumb.jpg)
![clip_image002[6] clip_image002[6]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_C821/clip_image0026_thumb.jpg)
![clip_image001[10] clip_image001[10]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_C821/clip_image00110_thumb.jpg)
![clip_image001[12] clip_image001[12]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_C821/clip_image00112_thumb.jpg)
![clip_image002[8] clip_image002[8]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_C821/clip_image0028_thumb.jpg)
![clip_image001[14] clip_image001[14]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_C821/clip_image00114_thumb.jpg)
![clip_image001[16] clip_image001[16]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_C821/clip_image00116_thumb.jpg)
![clip_image001[18] clip_image001[18]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_C821/clip_image00118_thumb.jpg)
![clip_image001[20] clip_image001[20]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70412Dump_C821/clip_image00120_thumb.jpg)
![clip_image001[4] clip_image001[4]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E6F3/clip_image0014_thumb.jpg)
![clip_image001[6] clip_image001[6]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E6F3/clip_image0016_thumb.jpg)
![clip_image002[4] clip_image002[4]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E6F3/clip_image0024_thumb.jpg)
![clip_image001[8] clip_image001[8]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E6F3/clip_image0018_thumb.jpg)
![clip_image001[10] clip_image001[10]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E6F3/clip_image00110_thumb.jpg)
![clip_image001[12] clip_image001[12]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E6F3/clip_image00112_thumb.jpg)
![clip_image001[4] clip_image001[4]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E5CE/clip_image0014_thumb.jpg)
![clip_image002[4] clip_image002[4]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E5CE/clip_image0024_thumb.jpg)
![clip_image002[6] clip_image002[6]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E5CE/clip_image0026_thumb.jpg)
![clip_image002[8] clip_image002[8]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E5CE/clip_image0028_thumb.jpg)
![clip_image001[12] clip_image001[12]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E5CE/clip_image00112_thumb.jpg)
![clip_image002[4] clip_image002[4]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E3F9/clip_image0024_thumb.jpg)
![clip_image002[6] clip_image002[6]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E3F9/clip_image0026_thumb.jpg)
![clip_image002[8] clip_image002[8]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E3F9/clip_image0028_thumb.jpg)
![clip_image002[10] clip_image002[10]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E3F9/clip_image00210_thumb.jpg)
![clip_image002[12] clip_image002[12]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E3F9/clip_image00212_thumb.jpg)
![clip_image002[14] clip_image002[14]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E3F9/clip_image00214_thumb.jpg)
![clip_image002[16] clip_image002[16]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E3F9/clip_image00216_thumb.jpg)
![clip_image001[4] clip_image001[4]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E3F9/clip_image0014_thumb.jpg)
![clip_image001[6] clip_image001[6]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E3F9/clip_image0016_thumb.jpg)
![clip_image001[8] clip_image001[8]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E3F9/clip_image0018_thumb.jpg)
![clip_image001[10] clip_image001[10]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E3F9/clip_image00110_thumb.jpg)
![clip_image001[12] clip_image001[12]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E3F9/clip_image00112_thumb.jpg)
![clip_image001[14] clip_image001[14]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E3F9/clip_image00114_thumb.jpg)
![clip_image001[16] clip_image001[16]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E3F9/clip_image00116_thumb.jpg)
![clip_image002[18] clip_image002[18]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E3F9/clip_image00218_thumb.jpg)
![clip_image002[20] clip_image002[20]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E3F9/clip_image00220_thumb.jpg)
![clip_image001[18] clip_image001[18]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E3F9/clip_image00118_thumb.jpg)
![clip_image002[22] clip_image002[22]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E3F9/clip_image00222_thumb.jpg)
![clip_image002[4] clip_image002[4]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E0BA/clip_image0024_thumb.jpg)
![clip_image002[6] clip_image002[6]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E0BA/clip_image0026_thumb.jpg)
![clip_image002[8] clip_image002[8]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E0BA/clip_image0028_thumb.jpg)
![clip_image002[10] clip_image002[10]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E0BA/clip_image00210_thumb.jpg)
![clip_image002[12] clip_image002[12]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E0BA/clip_image00212_thumb.jpg)
![clip_image002[14] clip_image002[14]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E0BA/clip_image00214_thumb.jpg)
![clip_image002[18] clip_image002[18]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E0BA/clip_image00218_thumb.jpg)
![clip_image001[4] clip_image001[4]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E0BA/clip_image0014_thumb.jpg)
![clip_image001[6] clip_image001[6]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_E0BA/clip_image0016_thumb.jpg)
![clip_image001[4] clip_image001[4]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D3F6/clip_image0014_thumb.jpg)
![clip_image001[6] clip_image001[6]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D3F6/clip_image0016_thumb.jpg)
![clip_image001[8] clip_image001[8]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D3F6/clip_image0018_thumb.jpg)
![clip_image001[10] clip_image001[10]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D3F6/clip_image00110_thumb.jpg)
![clip_image001[12] clip_image001[12]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D3F6/clip_image00112_thumb.jpg)
![clip_image001[14] clip_image001[14]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D3F6/clip_image00114_thumb.jpg)
![clip_image002[4] clip_image002[4]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D3F6/clip_image0024_thumb.jpg)
![clip_image002[6] clip_image002[6]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D3F6/clip_image0026_thumb.jpg)
![clip_image002[8] clip_image002[8]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D3F6/clip_image0028_thumb.jpg)
![clip_image002[10] clip_image002[10]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D3F6/clip_image00210_thumb.jpg)

![clip_image002[4] clip_image002[4]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D221/clip_image0024_thumb.jpg)
![clip_image002[6] clip_image002[6]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D221/clip_image0026_thumb.jpg)
![clip_image002[8] clip_image002[8]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D221/clip_image0028_thumb.jpg)
![clip_image002[10] clip_image002[10]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D221/clip_image00210_thumb.jpg)
![clip_image002[12] clip_image002[12]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D221/clip_image00212_thumb.jpg)
![clip_image002[14] clip_image002[14]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D221/clip_image00214_thumb.jpg)


![clip_image002[4] clip_image002[4]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D028/clip_image0024_thumb.jpg)
![clip_image002[6] clip_image002[6]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D028/clip_image0026_thumb.jpg)
![clip_image002[8] clip_image002[8]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D028/clip_image0028_thumb.jpg)
![clip_image001[4] clip_image001[4]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D028/clip_image0014_thumb.jpg)
![clip_image002[10] clip_image002[10]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D028/clip_image00210_thumb.jpg)
![clip_image002[12] clip_image002[12]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D028/clip_image00212_thumb.jpg)
![clip_image002[14] clip_image002[14]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D028/clip_image00214_thumb.jpg)
![clip_image001[6] clip_image001[6]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D028/clip_image0016_thumb.jpg)
![clip_image001[8] clip_image001[8]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D028/clip_image0018_thumb.jpg)
![clip_image001[10] clip_image001[10]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D028/clip_image00110_thumb.jpg)
![clip_image001[12] clip_image001[12]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D028/clip_image00112_thumb.jpg)
![clip_image001[14] clip_image001[14]](http://examgod.com/l2pimages/Official2014LatestFreeMicrosoft70341Dump_D028/clip_image00114_thumb.jpg)